A digital identity platform is an infrastructure that manages digital credentials, authentication, authorisation, and compliance across digital services. In 2026, identity functions as the primary security layer in regulated digital environments. Especially in Singapore, identity platforms are frequently utilised for financial onboarding, government e-services, healthcare systems, and cross-border trade.
What Is a Digital Identity Platform?
A digital identity platform is a system that creates, verifies, stores, and manages digital identities for individuals and organisations. It replaces fragmented login systems and manual verification processes with a unified identity framework.
A digital identity consists of verified attributes such as:
- Legal name
- Date of birth
- Identification number
- Biometric markers
- Organisational roles
- Licensing or credential status
The platform acts as the infrastructure layer that securely validates and transmits these attributes when required. In Singapore, identity frameworks operate alongside national systems such as Singpass, managed by GovTech.
Core Architecture of a Digital Identity Platform
A modern enterprise-grade platform typically consists of five core elements:
1. Identity Proofing Engine
- OCR-based document validation
- Biometric facial matching
- Liveness detection
- Database cross-checking
2. Credential Management System (CMS)
- Stores issued credentials
- Tracks revocation status
- Manages lifecycle events
3. Authentication Services
- Multi-Factor Authentication (MFA)
- FIDO2 passwordless authentication
- Biometric logins
- Risk-based authentication

4. Authorisation & Policy Engine
- Role-Based Access Control (RBAC)
- Attribute-Based Access Control (ABAC)
- Least privilege enforcement
5. Audit & Compliance Layer
- Immutable logs
- Access monitoring
- Regulatory reporting
This structure enables scalable identity verification across financial institutions, healthcare providers, educational institutions, and government systems.
How a Digital Identity Platform Works
Operationally, the system follows a four-stage lifecycle:
Stage 1: Identity Proofing
Verification of government-issued documentation and biometric confirmation.
Stage 2: Credential Issuance
Creation of a secure digital credential stored in:
- Encrypted cloud servers
- Hardware security modules
- Mobile digital wallets
Stage 3: Authentication
Verification of user presence and intent during each access attempt.
Stage 4: Authorisation
System-based rules determine permissible access to systems or data.
This model supports both centralised and decentralised identity structures.
Centralised vs Decentralised Identity (DID)
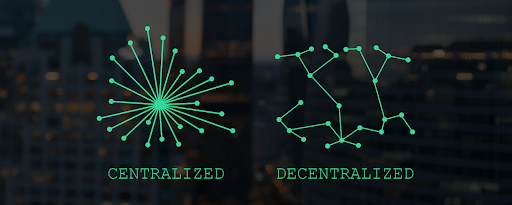
Centralised Identity Model
Identity data is stored and controlled by a single provider (e.g., a bank or enterprise IAM system). This increases the chance of risk exposure to high-impact data breaches and single point of failure.
Decentralised Identity (DID)
Decentralised Identity (DID) allows users to control credentials within private wallets rather than relying solely on a central authority. DID systems rely on standards developed by organisations such as the World Wide Web Consortium and the OpenID Foundation.
This model aligns with Self-Sovereign Identity (SSI) frameworks, gaining adoption in 2026.
Blockchain-Based Identity Systems
Blockchain-based identity systems such as those developed by Trident Digital Technology, uses distributed ledger technology (DLT) to record verification events without storing raw personal data on-chain. Key characteristics include:
- Cryptographic signatures
- Tamper-resistant verification records
- Decentralised validation nodes
- Time-stamped audit trails
These systems are particularly relevant for cross-border trade within frameworks supported by the Association of Southeast Asian Nations digital economy initiatives.
Regulatory and Compliance Framework in Singapore
Digital identity platforms operating in Singapore must align with:
Governs data collection, usage, and disclosure.
- MAS Technology Risk Management (TRM) Guidelines
Issued by the Monetary Authority of Singapore for financial institutions.
- Cybersecurity Act
Regulates Critical Information Infrastructure (CII) providers.
- IMDA Governance Requirements
Under the Infocomm Media Development Authority for digital service providers. To maintain compliance, platforms must implement:
- AES-256 encryption (data at rest)
- TLS 1.3 encryption (data in transit)
- Immutable audit logs
- Role-based internal access restrictions
- Data residency controls
Industry Applications in Singapore

Financial Services
Digital identity platforms support automated KYC and AML processes, enabling faster compliance checks and reducing manual verification. They also facilitate secure remote onboarding and legally recognised digital signatures for seamless customer transactions.
Healthcare
They enable controlled access to patient records, ensuring that only authorised personnel can view sensitive medical data. Digital identity systems also help verify practitioner credentials to maintain trust and regulatory compliance.
Education
Institutions use digital identity solutions to issue verifiable digital diplomas that can be easily shared and authenticated. They also support cross-border academic recognition by providing tamper-proof credential verification.
Government
National e-services depend on secure identity authentication frameworks such as Singpass to provide citizens with safe and convenient access to public services online.
Privacy and User Control
Modern digital identity platforms integrate Privacy Enhancing Technologies (PETs) such as selective disclosure, which allows users to prove eligibility (for example, confirming they are over 18) without revealing their full birthdate.
They also use zero-knowledge proofs to verify claims without exposing raw data, alongside consent management dashboards that let users grant or revoke access to their information. This approach minimises unnecessary data exposure while maintaining regulatory compliance.
Implementation Considerations for Enterprises
Organisations evaluating a digital identity platform should assess:
- Legacy Integration: Compatibility with HR, ERP, CRM, and IAM systems.
- Scalability: Capability to process millions of authentication requests.
- Data Residency: Local storage requirements under Singapore law.
- Risk and Insurance Implications: Impact on cyber liability exposure.
- Vendor Lock-In Risk: Portability of credentials across providers.
Common Challenges
Despite their benefits, digital identity platforms come with several operational and regulatory challenges:
- Integration complexity – Connecting legacy systems with modern identity frameworks can be costly and time-consuming.
- Regulatory compliance – Navigating evolving data protection laws across jurisdictions requires continuous updates.
- User adoption barriers – Some users may resist new authentication methods due to usability concerns.
- Interoperability issues – Ensuring seamless identity verification across different platforms and borders remains complex.
- AI-driven phishing attacks – Advanced AI tools enable highly convincing phishing and social engineering attacks that can bypass traditional verification methods.
- Private key management risks – In decentralised systems, users are responsible for safeguarding private keys, and loss or compromise can result in permanent identity access issues.
The Future of Digital Identity Beyond 2026
Identity has become the primary security perimeter in digital ecosystems. Digital identity is expected to evolve alongside emerging technologies and global digital ecosystems:

- Decentralised identity models will give users greater control over their personal data while reducing reliance on centralised databases.
- Stronger cryptographic protocols will enhance data protection and safeguard digital credentials against emerging cyber threats.
- Advanced biometrics will enable more seamless and secure authentication experiences across devices and platforms.
- AI-driven fraud detection will proactively identify suspicious activity and prevent identity misuse in real time.
- Improved cross-border digital identity standards will support more secure global digital transactions, education, and government services.
FAQ
What is the difference between digital identity and a digital identity platform?
A digital identity refers to verified attributes about an individual or organisation. A digital identity platform is the infrastructure that manages, authenticates, and secures those attributes.
Is decentralised identity more secure than traditional systems?
Generally yes, decentralised identity reduces breach risks associated with centralised platforms since users control their own credentials.
Can digital identity platforms work internationally?
Yes, if built on recognised open standards such as W3C Verifiable Credentials and OIDC.
Are digital identity platforms scalable for growing organisations?
Yes, they are built to scale alongside business growth and increasing user demands.
Why are digital identity platforms important in 2026?
They protect sensitive data, prevent cyber threats, and enable seamless digital experiences across connected systems.
Conclusion
A digital identity platform such as Tridentity provides the infrastructure necessary for secure, compliant, and scalable digital interactions. In Singapore’s regulated environment, identity verification is a great asset in 2026, especially for financial services, healthcare systems, education, and government services.
With evolving cyber threats and security concerns, organisations operating in regulated or high-trust environments can support better compliance, security, documentation, and workplace efficiency by integrating decentralised identity models and blockchain-based verification systems to their workplaces.
Evaluate your digital identity infrastructure today! Talk to Us



